The Future of Automation: A Journey Towards Autonomous Systems.
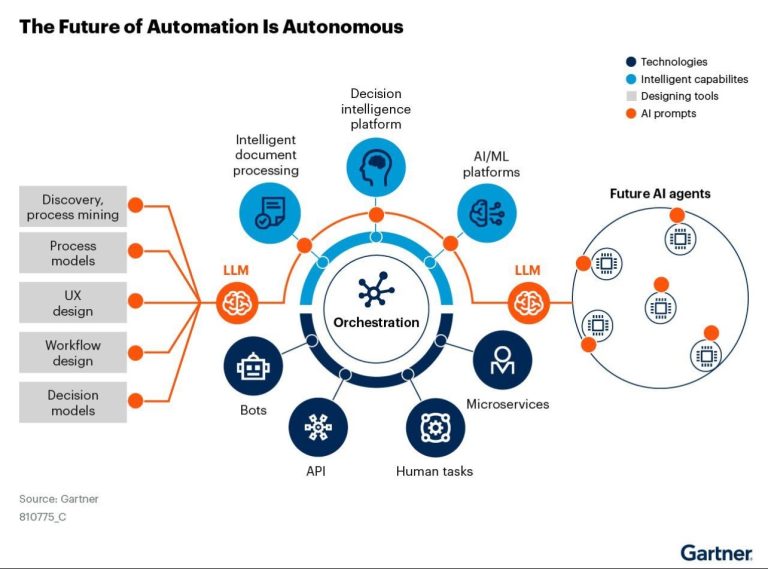
The image below offers a fascinating glimpse into the automation process, a journey that is fundamentally transforming the way we work.
- “Every major technological revolution has disrupted the job market. The Agricultural Revolution turned hunter-gatherers into farmers, the Industrial Revolution turned farmers into factory workers, and the Information Revolution is turning factory workers into knowledge workers and service providers.” (Yuval Noah Harari, Sapiens: A Brief History of Humankind)
The journey depicted in the image is a map, not a destination. By understanding the stages of automation, leveraging the power of cloud computing, and learning from the past, we can ensure that automation empowers us to build a future of work that is both efficient and fulfilling.
Let’s see how we can achieve this with minimal impact on what defines human nature, particularly utility.
Automation has evolved significantly over the past few decades, moving from simple mechanization to advanced intelligent systems. The image titled “The Future of Automation Is Autonomous,” sourced from Gartner, provides a comprehensive overview of the components and processes involved in achieving autonomous automation. This article explores the various elements depicted in the diagram, shedding light on how businesses can leverage these technologies to streamline operations, enhance decision-making, and foster innovation.
In discussing the transformative power of automation, it’s essential to draw parallels with historical moments that reshaped society and work, much like the advent of the Industrial Revolution. Books such as “The Fourth Industrial Revolution” by Klaus Schwab and “The Second Machine Age” by Erik Brynjolfsson and Andrew McAfee, offer profound insights into these shifts.
Core Elements of Automation
1.Discovery and Process Mining:
This initial step involves identifying and analyzing existing business processes. Process mining tools help uncover inefficiencies, bottlenecks, and opportunities for improvement by analyzing data from various sources. This foundational layer is crucial for understanding the current state of operations and setting the stage for automation.
“The Fourth Industrial Revolution” by Klaus Schwab gives a deeper understanding of how technological advancements historically disrupt and redefine industries. Schwab discusses how the digital revolution, much like the industrial revolution, necessitates a re-evaluation of existing processes and workflows. Process mining, in this context, is akin to the early stages of industrialization, where understanding the existing landscape was critical for implementing mechanization.
2. Process Models:
Once processes are identified, they are documented and modeled. Process models serve as blueprints for automation, detailing the workflow, tasks, and decision points involved. These models are essential for designing automation solutions that align with business objectives.
In the book “The Second Machine Age”, Brynjolfsson and McAfee highlight the significance of digital models and blueprints in enabling automation. They argue that “just as the steam engine and electricity freed labor from physical tasks, digital technologies are now freeing knowledge workers from cognitive tasks.” This resonates with the function of process models in modern automation, setting the stage for machines to take over complex decision-making tasks.
3. UX Design:
User Experience (UX) design focuses on creating intuitive and efficient interfaces for interacting with automated systems. Good UX design ensures that users can easily navigate and use the systems, enhancing productivity and user satisfaction.
The emphasis on UX design in automation parallels the user-centric approaches discussed in “The Lean Startup” by Eric Ries. Just as Ries emphasizes the importance of feedback loops in product development, UX design in automation must continuously evolve based on user feedback to remain effective and relevant.
4. Workflow Design:
Workflow design involves structuring the sequence of tasks and activities to optimize efficiency. In an automated system, workflows are designed to minimize manual intervention, reduce errors, and accelerate task completion.
In the book “The Innovator’s Dilemma”, Clayton Christensen analyzes the business process innovation, emphasizing the need for companies to adapt their workflows to leverage disruptive technologies. He notes that “established companies often fail to capitalize on new technologies because they are not integrated into existing workflows.” This insight underscores the importance of proactive workflow design in adopting automation technologies.
5. Decision Models:
Decision models define the criteria and rules for automated decision-making. These models are essential for systems that need to make decisions based on data inputs, such as determining the next steps in a process or identifying exceptions.
Reflecting on “Thinking, Fast and Slow” by Daniel Kahneman, decision models in automation mirror the interplay between the brain’s fast and slow thinking processes. Automation often takes over the “fast thinking” tasks, allowing human workers to focus on more complex, “slow thinking” decisions, thus enhancing overall efficiency and decision quality.
Intelligent Capabilities and Future Implications
As automation technology continues to evolve, it incorporates intelligent capabilities such as AI and machine learning, as discussed in “Superintelligence” by Nick Bostrom. Bostrom’s exploration of the potential of AI to surpass human intelligence highlights the critical role that these technologies will play in future automation.
The integration of AI and machine learning into automation, as depicted in the Gartner image, echoes Bostrom’s predictions about the transformative potential of superintelligent systems. These technologies enable businesses to automate not just routine tasks but also complex decision-making processes, pushing the boundaries of what is possible with automation.
In conclusion, the journey towards autonomous automation is akin to significant historical shifts in industry and society. By drawing from books such as “The Fourth Industrial Revolution”, “The Second Machine Age”, and “Superintelligence” we can better understand the transformative impact of automation technologies. As businesses continue to adopt and integrate these technologies, they must remain agile, innovative, and responsive to the ever-changing landscape of digital transformation. These insights not only enrich our understanding of automation but also prepare us for the opportunities and challenges that lie ahead.