The Cloud Migration Crossroads: A Modern Business Revolution with Historical Roots
In the ever-evolving landscape of technology, businesses constantly face the decision of whether to migrate their operations from on-premises infrastructures to cloud computing environments. This decision is akin to the monumental shifts in industry and economy chronicled in history books such as “Guns, Germs, and Steel” by Jared Diamond. Just as those great decisions shaped the future of humankind, the choice to transition to the cloud can significantly impact the trajectory of a business. Here’s a comprehensive guide to understanding when it’s the right time to make this leap, the advantages and disadvantages of cloud migration, and the historical parallels that underscore its importance.
The Winds of Change: When to Embrace the Cloud:
- Scalability Needs: If your business is experiencing rapid growth or unpredictable demand, the scalability offered by cloud services can be invaluable. Unlike on-premises systems, cloud infrastructure can be easily scaled up or down based on your requirements.
- Cost Management: When the costs of maintaining and upgrading on-premises hardware and software become prohibitive, migrating to the cloud can offer significant savings. Cloud services operate on a pay-as-you-go model, which can help manage and reduce overall IT expenses.
- Remote Workforce: The rise of remote work has made cloud computing more relevant than ever. If your business has a distributed workforce, cloud solutions can provide seamless access to essential tools and data from anywhere in the world.
- Security Concerns: Modern cloud providers invest heavily in security measures and compliance certifications. If your business faces escalating security threats or compliance requirements, the advanced security features of cloud platforms can provide peace of mind.
- Disaster Recovery: The ability to quickly recover from a disaster is crucial for business continuity. Cloud services typically offer robust disaster recovery options that can minimize downtime and data loss.
Pros of Cloud Migration:
- Flexibility and Scalability: Cloud computing offers unparalleled flexibility, allowing businesses to scale resources up or down as needed.
- Cost Efficiency: Reduces the need for significant capital expenditure on hardware and infrastructure. Operational expenses are more predictable and manageable.
- Enhanced Collaboration: Facilitates better collaboration among teams, especially in remote work scenarios, with real-time access to data and applications.
- Advanced Security: Leverages the sophisticated security protocols and compliance standards of cloud providers.
- Automatic Updates: Ensures that your software and infrastructure are always up-to-date without the need for manual intervention.
Nothing is 100% good or bad, so there are some disadvantages. However, these are not significant enough to outweigh the overall benefits. These drawbacks are more like occasional side effects, similar to those of a medical treatment. We are aware of the potential ‘blind spots’ and through our consultancy, we can greatly minimize their impact.
Cons of Cloud Migration:
- Dependency on Internet: Cloud services require a reliable internet connection. Downtime or connectivity issues can disrupt access to essential services.
- Data Privacy Concerns: Storing sensitive data off-premises raises concerns about privacy and control. Businesses must ensure that their cloud provider complies with relevant data protection regulations.
- Potential Downtime: While rare, cloud service outages can occur, potentially impacting business operations.
- Migration Complexity: The process of migrating to the cloud can be complex and time-consuming, requiring careful planning and execution.
Learning from Great Decisions:
In “Guns, Germs, and Steel,” Jared Diamond explores how the decisions to adopt agriculture, metallurgy, and other technological advancements transformed societies and economies. Similarly, the decision to migrate to the cloud represents a transformative step for modern businesses. Just as early societies weighed the benefits and risks of adopting new technologies, contemporary businesses must carefully consider the timing and implications of cloud migration.
Industrial Revolution: The shift from manual labor to mechanized production during the Industrial Revolution is analogous to moving from on-premises to cloud computing. Both transitions involve embracing new technologies to achieve greater efficiency and scalability.
Economic Shifts: The global economy’s move from agricultural to industrial and now to information-based paradigms reflects the ongoing evolution in business operations. Cloud computing is the latest frontier in this progression, offering new ways to leverage information and technology.
Cloud Computing: A Brief History and Evolution
The concept of cloud computing has roots that trace back several decades. Here’s a brief overview of its evolution:
- 1960s – The Foundation: The idea of time-sharing, where multiple users share computing resources, laid the groundwork for cloud computing. Companies like IBM and DEC developed mainframe computers that could be accessed by multiple users simultaneously.
- 1990s – The Internet Era: The rise of the internet in the 1990s enabled remote access to data and applications, setting the stage for cloud computing. Salesforce.com, launched in 1999, became one of the first companies to deliver applications over the internet, pioneering the concept of Software as a Service (SaaS).
- 2000s – Cloud Emergence: Amazon Web Services (AWS) launched in 2006 with its Elastic Compute Cloud (EC2) service, marking a significant milestone in cloud computing. This era saw the introduction of Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) models, enabling businesses to access computing resources on demand.
- 2010s – Mainstream Adoption: The 2010s saw widespread adoption of cloud services, with major players like Microsoft Azure, Google Cloud Platform, and IBM Cloud entering the market. Businesses began migrating critical workloads to the cloud, driven by the promise of scalability, cost savings, and flexibility.
- 2020s – Advanced Technologies and AI: The current decade is characterized by the integration of advanced technologies like artificial intelligence (AI), machine learning (ML), and the Internet of Things (IoT) into cloud services. Cloud providers are continuously enhancing their offerings to include sophisticated analytics, automation, and security features.
The Path Forward – A Calculated Risk:
In the words of historian Yuval Noah Harari, “The most important thing is to be able to constantly learn and change.” As with the great decisions of the past, the choice to migrate to the cloud isn’t without risk. Yet, with careful planning, thorough research, and a willingness to adapt, the cloud can empower businesses to thrive in the digital age, much like the Industrial Revolution propelled those who embraced its innovations.
Determining the right time to migrate your business to the cloud involves assessing your current needs, future growth prospects, and the specific advantages and disadvantages of cloud solutions. By drawing parallels to historical decisions that shaped human progress, it becomes clear that embracing cloud computing can position your business for greater flexibility, efficiency, and resilience in the face of modern challenges. Just as the great decisions of the past forged new paths for societies, the decision to migrate to the cloud can pave the way for your business’s future success.
Cybersecurity trends in 2024 – AI: friend or foe?
„60% of Romanian companies do not invest in cyber security. Education and a more vigorous action from the authorities are needed to increase awareness and investments in this area” – a conclusion that says a lot about strategic thinking and prevention and, why not, about a possible risk of undermining the national economy in the context of a cyber attack including targeting state institutions.
Ziarul Financiar’s 2024 cybersecurity event highlighted a rapidly evolving landscape, shaped by technological advancements like artificial intelligence (AI) and a growing array of threats. To ensure robust cybersecurity in this dynamic environment, businesses must adapt their laws, procedures, IT solutions, and managed IT services.
Here’s a breakdown of the main ideas discussed at the event and how they shape the cybersecurity landscape of today.
Legal Frameworks and Procedures – bring with it the possibility to measure:
New and updated regulations are emerging to address the unique challenges posed by AI and increasingly sophisticated cyberattacks. Companies must stay informed about these legal developments and ensure their cybersecurity practices comply with relevant laws. This involves understanding data protection requirements, incident reporting obligations, and liability frameworks.
Effective cybersecurity in 2024 necessitates comprehensive and adaptable procedures, such as:
- Incident Response Plans: Robust incident response plans enable swift and effective action in case of a breach. These plans must be regularly reviewed and updated to reflect the latest threats and technologies.
- Employee Training: Regular employee training on cybersecurity best practices is essential. This includes educating employees about phishing scams, social engineering tactics, and the importance of strong passwords.
- Security Audits: Routine security audits help identify vulnerabilities and weaknesses in a company’s cybersecurity posture. These audits can be conducted internally or by external cybersecurity experts.
IT Solutions:
Advanced IT solutions play a crucial role in safeguarding against modern cyber threats. Key technologies include:
- AI-Powered Security Tools: AI can be leveraged to detect and respond to threats in real-time, analyze vast amounts of security data, and identify patterns that could indicate an attack.
- Threat Intelligence Platforms: These platforms gather information about emerging threats and vulnerabilities, enabling organizations to address potential risks proactively.
- Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring users to provide multiple forms of identification to access sensitive systems and data.
Managed IT Services:
For many organizations, partnering with a managed IT services provider offers a cost-effective and efficient way to enhance cybersecurity. These providers can offer expertise, 24/7 monitoring, and access to advanced security tools that might be otherwise inaccessible.
The Double-Edged Sword of AI:
AI is a transformative technology that is both a tool for attackers and defenders in the cybersecurity realm.
AI in the Hands of Attackers:
- Advanced Phishing Attacks: AI can be used to create highly convincing phishing emails and websites, making it difficult for users to distinguish legitimate communications from malicious ones.
- Automated Attacks: AI can automate attacks, making them faster, more efficient, and harder to detect.
- Adaptive Malware: AI-powered malware can learn and evolve, making it more difficult to defend against.
AI in the Hands of Defenders:
- Threat Detection and Response: AI can analyze vast amounts of data to identify threats and vulnerabilities in real-time.
- Automated Security Operations: AI can automate routine security tasks, freeing up human analysts to focus on more complex threats.
- Predictive Analytics: AI can predict future cyberattacks, allowing organizations to proactively take steps to mitigate risks.
In 2024, cybersecurity is a multifaceted challenge that requires a comprehensive approach. By staying informed about the latest threats, adopting robust procedures, leveraging advanced IT solutions, and considering managed IT services, businesses can navigate this complex landscape and protect themselves from evolving cyber threats. The responsible and strategic use of AI will be pivotal in shaping the future of cybersecurity, tipping the scales in favor of defenders.
Here is a positive example of an attitude that each of us can adopt, in terms of corporate social responsibility – https://www.youtube.com/watch?v=vPa03SPTVCc, from a company you wouldn’t expect to have this approach – Catena.
BIC SA – A Legacy of Simplicity and Innovation in a Digital Age: Investing in Technology for the Future

Can you imagine selling 100,000,000,000 units of a product?
Well, what I can’t even begin to imagine, BIC turned into reality…
And that was 18 years ago when they sold their 100 billionth BIC ballpoint pen (the one you see in the picture).
So, let’s say that 79 years ago you created the most popular pen in history. It’s been selling at 50+ units per second ever since.
How do you innovate?
Do you change it and push something else on stage? Or do you change what goes on behind the curtain?
Wait! Hold that thought.
First, let me give you the context…
BIC SA, a global leader in writing instruments, lighters, and shavers, has created ingeniously simple and joyful products for over 79 years.
With a presence in more than 160 countries, the company has maintained its commitment to providing high-quality, affordable products to consumers worldwide.
As BIC celebrates its rich history, it also invests heavily in technology, from cloud computing and cybersecurity to artificial intelligence (AI), demonstrating its dedication to innovation and growth.
BIC’s success story began in 1945 when it established its presence in Belgium, with the invention of the world’s first disposable ballpoint pen by Marcel Bich. This revolutionary product quickly gained popularity due to its smooth writing experience, affordability, and convenience.
Since then, the company has expanded to various regions, including Italy, the Netherlands, Austria, Switzerland, Spain, and South America.
BIC SA’s iconic products, such as the BIC® M10® ballpoint pen, were introduced in 1956, marking a significant milestone in the company’s growth.
Over the years, BIC SA has continued to innovate and expand its product offerings, entering new markets and acquiring notable brands like Conté and Tipp-Ex, all of which embody the company’s commitment to quality and value for money.
In addition to its focus on innovation, BIC is committed to sustainability. The company has implemented several initiatives to reduce its environmental impact, such as using recycled materials and minimizing waste. These efforts reflect BIC’s commitment to operating responsibly and creating a sustainable future.
Despite its long-standing history, BIC SA is not resting on its laurels. The company is investing heavily in technology to support its strategic objectives and ensure its readiness for the future.
BIC SA’s recent job posting for a Senior Manager, Enterprise IT Infrastructure Architect, highlights its commitment to embracing cutting-edge technologies.
The role includes responsibilities such as:
- Active Directory Future State: Develop a strong identity and access management program in partnership with the Cybersecurity team.
- Physical Environment Consolidation: Employing a cloud-first approach to shrink the BIC enterprise’s physical footprint.
- Azure Architecture Refinement: Focusing on governance, security, and effective administration.
- Partnering with Cybersecurity to Develop a Device Management Strategy.
- The Development of AI Standards and Practices: Ensuring BIC is ready to move into the future with AI.
- Backup Strategy Optimization: Eliminating duplicative technologies and defining enterprise standards for on-premises, Azure, and hosted solutions.
These responsibilities demonstrate BIC SA’s dedication to investing in technology and its commitment to staying ahead of the curve in the ever-evolving tech landscape.
Also, BIC’s commitment to innovation extends to its exploration of AI technologies. The company is currently researching ways to leverage AI to improve product development, optimize supply chains, and personalize marketing campaigns. These efforts demonstrate BIC’s forward-thinking approach and its desire to remain at the forefront of innovation in the digital age.
BIC’s story is an inspiring example of a company that has successfully adapted to the ever-changing technological landscape while staying true to its core values. By embracing innovation and investing in cutting-edge technologies, BIC has ensured its continued growth and success for future generations.
Regardless of the field of activity you belong to, the years of experience, or the challenges you face, technology will help you stay competitive, the immediate benefits being:
- streamline company operations
- enhance customer experience
- gain valuable insights into consumer behavior
- adoption of cloud computing will improve company agility and scalability
- cybersecurity initiatives will protect the company’s sensitive data and ensure the integrity of its online operations
So, what’s your excuse? Whatever it is, we can find solutions together.
How to prepare your EU business for the NIS2 Directive
The NIS 2 Directive (Directive (EU) 2022/2555) aims to enhance cybersecurity across various sectors by imposing stringent cybersecurity requirements and incident management obligations. It mandates entities to implement risk analyses, IT security policies, incident handling procedures, and more to mitigate cybersecurity threats effectively. Moreover, the directive emphasizes reporting obligations for potential incidents and allows coordinated vulnerability disclosure.
For companies leveraging cloud computing and managed IT services, compliance with NIS 2 is crucial to ensure robust cybersecurity measures and incident response capabilities. By adhering to NIS 2, organizations can enhance their security posture, fortify supply chain security, improve network security, and strengthen access control measures.
Additionally, aligning with NIS 2 requirements can increase cybersecurity awareness, preparedness, and resilience against cyber threats, ultimately safeguarding critical infrastructure and services.
The key cybersecurity measures required by the NIS 2 Directive include:
- Risk Analysis and Information System Security Policies: Organizations must conduct risk analyses and establish robust information system security policies to identify and mitigate cyber risks;
- Assessment of Cyber Risk Management Effectiveness: Entities are mandated to assess the effectiveness of their cyber risk management practices to ensure they are adequately protecting against cybersecurity threats;
- Business Continuity Planning: NIS 2 emphasizes the importance of having comprehensive business continuity plans in place to ensure operational resilience in the face of cyber incidents;
- Security Requirements and Reference Network Architecture: Implementing specific security requirements and establishing a reference network architecture are crucial components of complying with NIS 2 cybersecurity measures;
- Management Oversight and Cybersecurity Training: The directive requires management boards to oversee cyber risk management approaches and mandates cybersecurity training for employees to enhance overall security awareness;
- Supply Chain Security: Organizations must address vulnerabilities in their supply chain and ensure secure development practices to mitigate risks associated with third-party dependencies.
Cloud computing solutions offer cybersecurity benefits by enabling antifragility, a concept from Nassim Taleb’s book “Antifragile: Things That Gain from Disorder.” Antifragility in cybersecurity involves systems improving in response to stressors, shocks, and attacks, unlike resilience which maintains the status quo. Cloud computing infrastructures can be designed to be antifragile, gaining from disorder and becoming more robust with each challenge.
Organizations can become antifragile in their cybersecurity measures by adopting the following strategies:
- Lessons Learned: Implementing a robust Lessons Learned process is crucial for organizations to become antifragile. This involves analyzing past cybersecurity incidents, understanding how they occurred, and incorporating these insights into future defenses;
- Barbell Strategy: Nassim Taleb’s barbell strategy can be applied to cybersecurity. This approach combines hyper-conservative (fragile) and hyper-aggressive (antifragile) measures while minimizing anything in the middle (resilient). For example, using asymmetric encryption models with fragile private keys and antifragile public keys can help protect sensitive information;
- Purple Teaming: Conducting purple teaming exercises can help organizations become antifragile. This collaborative exercise between defenders and attackers allows for a better understanding of both attack and defense mechanisms, leading to improved cybersecurity measures;
- Autonomic Security Operations: Implementing autonomic security operations can help organizations become antifragile. By automatically analyzing activity data and learning from it, these systems can quickly identify and mitigate threats without human intervention;
- Visibility Engineering: Prioritizing efforts to build “muscle” in visibility engineering is essential for organizations to become antifragile. This involves designing and implementing mechanisms that capture and report asset data, helping to identify key assets worth protecting and their corresponding security vulnerabilities.
By adopting these strategies, organizations can move beyond mere resilience and become antifragile, actively learning and growing stronger from cybersecurity challenges.
Some basic protective measures for cybersecurity resilience include:
- Implementing Two-Factor Authentication: Utilize two-factor authentication to add an extra layer of security to user accounts, making it harder for unauthorized individuals to access sensitive information;
- Regularly Testing and Evaluating Systems: Conduct vulnerability assessments, penetration testing, and security audits regularly to identify weaknesses and gaps in systems. This proactive approach helps address vulnerabilities before attackers can exploit them;
- Establishing Encryption and Data Protection: Deploy robust encryption measures to protect data at rest and in transit. Implement stringent access controls, authentication protocols, and data classification frameworks to ensure the confidentiality, integrity, and availability of critical information;
- Developing a Robust Backup and Recovery Strategy: Prepare for worst-case scenarios by creating a comprehensive strategy for backing up and recovering data. Regularly back up critical data, conduct tests to ensure effective restoration processes, and consider utilizing off-site backups or cloud-based solutions for enhanced redundancy;
- Continuous Monitoring for Threats: Employ real-time monitoring systems that provide visibility into networks, systems, and applications. Utilize intrusion detection systems, security information, and event management (SIEM) tools, and log analysis to detect and respond to cyber threats promptly;
- Staying Informed: Stay current with cybersecurity trends, emerging threats, and regulatory changes by subscribing to industry newsletters, participating in webinars, following reputable cybersecurity blogs, and attending updated training sessions. Being well-informed empowers organizations to make informed decisions and adapt their cyber resilience strategy to evolving risks.
Some common cyber threats that organizations should be aware of include:
- Malware: Malware is a prevalent and persistent security threat that involves unwanted software installing itself on a system to cause harm, such as denying access, deleting files, stealing information, or spreading to other systems;
- Password Theft: Password theft occurs when unauthorized individuals steal or guess passwords to gain access to sensitive information. Attackers may use various methods like brute force attacks or social engineering to obtain passwords;
- Traffic Interception: Also known as eavesdropping, traffic interception involves a third party intercepting information sent between a user and a host. This stolen information can include log-ins or valuable data, which can be used maliciously;
- Phishing Attacks: Phishing scams rely on social engineering to trick individuals into revealing sensitive information like passwords. Attackers often send deceptive messages or emails that appear legitimate to obtain personal data;
- DDoS Attacks: Distributed Denial of Service (DDoS) attacks overload servers with user requests, causing websites to slow down or become inaccessible. These attacks disrupt normal operations by flooding servers with traffic;
- Insider Threats: Insider threats occur when individuals with authorized access intentionally or unintentionally compromise an organization’s security. This can include employees sharing sensitive data, falling victim to phishing attacks, or intentionally bypassing security measures;
- Advanced Persistent Threats (APTs): APTs are sophisticated and targeted cyberattacks that aim to steal data over an extended period without being detected. Detecting anomalies in outbound data and monitoring for unusual activities are crucial in combating APTs;
- Malvertising: Malvertising involves injecting malicious code into legitimate online advertising networks to redirect users to malicious websites or install malware on their devices. Ad networks should implement validation processes to reduce the risk of malvertising attacks.
By applying antifragility principles to cybersecurity, organizations can enhance their ability to thrive in the face of cyber threats, moving beyond mere resilience to actively improving and evolving in the face of adversity.
![]()
You can also read some of this information in Romanian-published in the Club IT&C magazine.
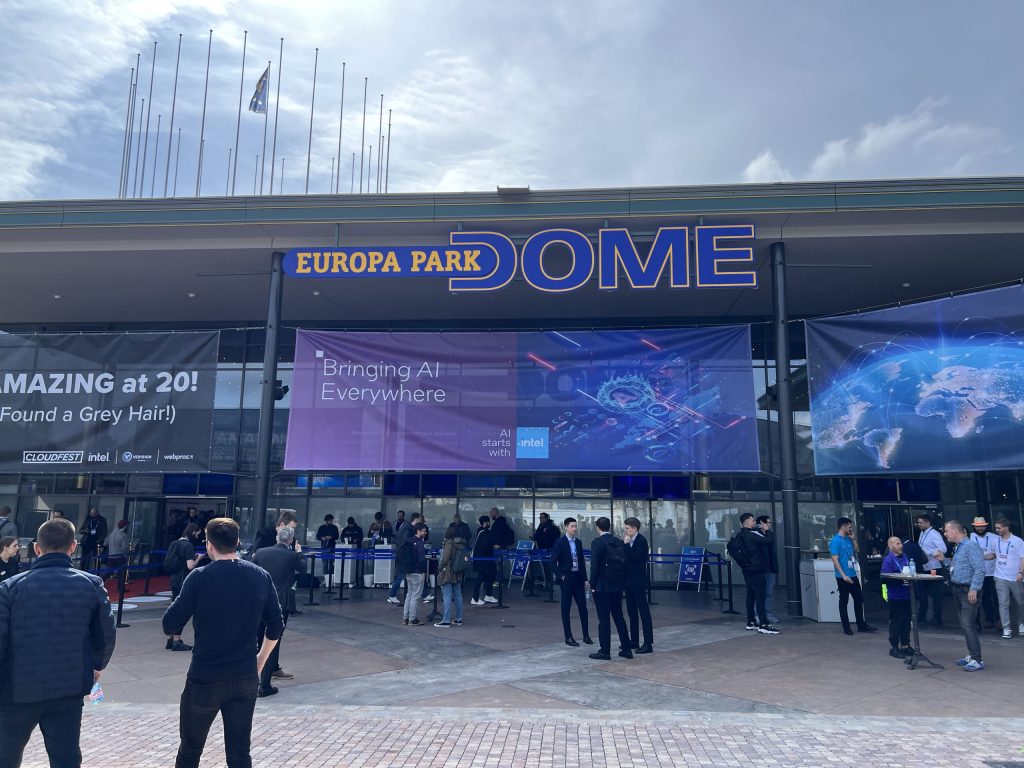
LifeinCloud on CloudFest 2024
When we entered the cloud computing industry, we felt like we had joined a global family. This feeling was reinforced when we attended CloudFest 2024, the world’s leading cloud industry conference.
Technology is a universal language that facilitates collaboration, innovation, and the creation of human bonds that may not be possible in other contexts, at least not so fast. At CloudFest 2024, the focus was not on competition or hard selling, but on addressing needs, technical issues, and mistakes. Everyone was open to listening to each other, helping each other, and forming long-term partnerships.

It was heartening to see that companies from Eastern Europe, such as StorePool from Bulgaria, Admin Tools from Romania, and a SuperMicro dealer from Serbia, were well-represented at the event.
Here’s a summary of the main ideas with which we left from this event, by category of interests, from hardware to cybersecurity:
Forced by the pandemic period to streamline production costs, hardware equipment suppliers have made a remarkable leap, a good example being Ampere Computing, a semiconductor company specializing in Cloud Native Processors, CPUs, and Data Center Solutions.
The company was founded in 2018 by Renée James, a semiconductor industry veteran. Ampere focuses on delivering high-performance, energy-efficient, and sustainable cloud computing solutions. Their innovative approach to CPU design emphasizes efficiency and performance for cloud, AI inferencing, and edge applications.
Product Technology Advantages of Ampere Computing:
- Cloud Native Processors: Ampere’s processors are designed for cloud-native applications, offering high performance and energy efficiency tailored for modern computing needs.
- Ampere Altra Family: This product line scales from 32 to 128 cores, providing an ideal mix of compute, memory, and I/O for various data center environments and edge deployments.
- AmpereOne Family: With an industry-leading 192 cores, the AmpereOne processors are built for hyperscale cloud deployments requiring extreme performance and core density.
- Efficiency and Sustainability: Ampere’s processors significantly reduce power consumption across all cloud infrastructures and workloads, especially in AI applications.
- Innovative Design: The processors feature fine-grained power management, memory tagging, DDR5 memory channels, and PCIe Gen5 IO lanes, and are manufactured on the 5nm process node for improved performance consistency, manageability, and security.
- Custom Core Design: The AmpereOne Family is based on a new custom core with 192 single-threaded cores designed to maximize performance at sustainable power levels.

Riedo Networks Ltd, a family-owned Swiss company, specializes in designing and manufacturing Power Distribution Units (PDUs) and Smart Meters for data centers and industrial markets.
Here is a summary of Riedo Networks Ltd’s products and technology advantages based on the provided sources:
- UPDU® Universal Power Distribution Unit: Riedo Networks offers the UPDU®, a slim and cost-effective PDU that stands out for its upgradeability and repairability after installation. This feature provides flexibility and cost-effectiveness to customers in managing their power distribution needs.
- Dual-Locking Power Cords: Riedo Networks sets the standard with dual-locking power cords, ensuring secure and reliable power connections within data centers and industrial environments.
- Smart Meters and Software: The company provides low-cost smart meters and software solutions that enhance energy monitoring and management capabilities for data centers and industrial markets, contributing to improved efficiency and cost savings.
Kevlarr is a company that specializes in AI-driven DMARC management for Managed Service Providers (MSPs) to protect online brands and identities against phishing, CEO fraud, impersonation, and other online threats. Their services focus on enhancing email security and scalability for businesses.
Key points about Kevlarr:
- AI-Driven DMARC Management: Kevlarr offers AI-driven DMARC management services to help MSPs protect their online brand and identity against online dangers like phishing and CEO fraud.
- Email Security Enhancement: The company assists in setting up secure email standards to ensure secure and scalable email services for businesses, helping them combat malicious activities like phishing and impersonation
The event not only provides a unique opportunity to connect with industry leaders and decision-makers but also fosters a sense of community and a shared vision for a more sustainable and equitable future in the IT sector. Overall, CloudFest 2024 equips participants with the tools, strategies, and connections needed to navigate the evolving landscape of the IT industry and contribute to building a stronger and more collaborative digital ecosystem.
For LifeinCloud it was a great opportunity to confirm that we are on the right track not only from a business perspective but also from people that we want to surround ourselves with.
More pictures:







Two Sides of the Cloud Coin
Cloud computing has brought about a significant change in the way businesses function. It offers scalable, flexible, and cost-effective solutions that have transformed traditional business models. Cloud computing allows businesses to access and store data over the internet, which means they don’t have to rely on physical hardware or on-premises data centers anymore.
Embark on the digital journey of your business with LifeInCloud: Discover the power of technology
Born out of a passion for innovation and a commitment to revolutionizing the IT landscape, LifeinCloud is your destination for next-generation cloud computing solutions and IT management services.